“They weren’t hiring staff. They were sourcing labour for a fraud factory.”
I’ve gone through the court filings, the seizure warrants, the satellite imagery, and the supporting intelligence tied to what’s now being called the Scam Center Strike Force investigations. This isn’t theory anymore — it’s now backed by a U.S.
Department of Justice press release confirming that authorities are actively targeting the same networks, the same infrastructure, and the same Southeast Asian scam compounds that this evidence points to.
And the deeper I’ve gone, the clearer it’s become that this is not just another layer of the scam economy — it’s the structure underneath it.
What most people see is the front end: a message, a relationship, an “investment opportunity.” What they don’t see is where that message is coming from, who is being forced to send it, and how organised the entire system really is.
Because once you strip it back properly — not just the websites, but the infrastructure behind them — you’re left with something far more serious than online fraud.
You’re looking at coordinated, industrial-scale operations built on human exploitation — where trafficked individuals are forced to run scams at scale, and where entire compounds exist for the sole purpose of extracting money from victims around the world.
The turning point: when fraud meets trafficking
Up until recently, most discussions around crypto scams focused on the financial side — how people are tricked, how money is moved, how platforms are faked. That’s still relevant, but it’s incomplete.
The material tied to this investigation makes something very clear:
these scams are being powered by a workforce that is, in many cases, trafficked into place.
According to the FBI affidavit supporting the seizure of scam-linked domains, individuals are routinely lured with legitimate job offers, often in tech or customer service roles, and transported to locations near the Thai–Myanmar border.
Once they arrive, the situation changes completely.
Passports are taken. Movement is restricted. And instead of legitimate work, they are placed inside scam compounds and told to start contacting targets overseas. The transition from “job opportunity” to forced participation in fraud is not gradual — it’s immediate.
This isn’t speculation or anecdotal reporting. It’s documented within a federal investigation that ties these labour pipelines directly into the same infrastructure used to defraud victims.
The compounds are real — and they are expanding
The term “compound” can sound abstract until you actually see the evidence. The investigation doesn’t just reference these locations — it maps them, tracks their development, and shows how quickly they’ve grown.
The Tai Chang compound, also known as Ko Sai Casino, is one of the central locations identified. What stands out immediately is the scale. Satellite imagery included in the affidavit shows a clear progression from undeveloped land in 2020 to a multi-structure facility by 2025, with distinct zones and expansion into additional nearby compounds.
And it doesn’t stop there.
Investigators identified at least three separate but related sites:
- Tai Chang 1.0 (the main operational hub)
- Tai Chang 2.0 (a newer compound under development)
- Tai Chang 3.0 (another expansion site with infrastructure already in place)
This isn’t a static operation. It’s growing.
What’s particularly telling is that these expansions appear to coincide with increased scrutiny and enforcement. As pressure builds, the response isn’t to shut down — it’s to relocate, duplicate, and continue operating.
That’s not the behaviour of a fragile system.
That’s a system designed to survive.
Control, protection, and the criminal ecosystem
One of the more uncomfortable realities in this case is who controls the environment these compounds operate in.
The affidavit links the Tai Chang compounds to territory controlled by the Democratic Karen Benevolent Army (DKBA), alongside Chinese criminal networks.
That combination matters.
Because it means these operations are not just tolerated — they are effectively protected within controlled regions, where local enforcement either cannot or will not intervene.
The surrounding area reinforces this point. Investigators identified:
- Drug production facilities within a few miles of the compounds
- The residence of a senior militia leader nearby
- Infrastructure that supports long-term occupation and operation
When you step back and look at it properly, what you’re seeing is not a single criminal enterprise, but a cluster of interconnected activities operating within the same geographic and power structure.
Fraud. Trafficking. Drug production.
All within the same ecosystem.
The workforce: recruited, trapped, and controlled
Understanding how people end up inside these compounds is critical, because it explains how the system sustains itself.
The recruitment process is consistent across multiple documented cases:
- Advertisements for high-paying jobs
- Offers targeting individuals in countries like Malaysia, India, and parts of Africa
- Travel arrangements handled by intermediaries
But once the individual reaches the region, the situation changes rapidly.
They are moved across borders — often into Myanmar — and placed inside secured compounds. From that point on, they are no longer free to leave.
The affidavit references victims being housed in multi-story buildings with hundreds of people per floor, all assigned to carry out scam operations targeting overseas victims.
What keeps them there is not employment.
It’s control.
- Physical violence
- Threats
- Debt bondage
- Ransom demands to families
In one documented case, an individual who refused to participate was beaten and thrown from a building, only being released after a ransom was paid.
This is not a grey area.
This is coercion being used to sustain fraud at scale.
The role of the Scam Center Strike Force
This is where the narrative shifts again — because this isn’t going unnoticed.
The formation of the Scam Center Strike Force in 2025 marks a coordinated response at a level we haven’t really seen before. This isn’t one agency working in isolation. It’s a combined effort involving:
- The Department of Justice
- The FBI
- The U.S. Secret Service
- Treasury and international partners
Their focus is very specific:
- Target the infrastructure behind these compounds
- Seize domains and disrupt digital operations
- Trace and restrain cryptocurrency flows
- Identify and pursue the individuals running these networks
And the numbers tell their own story.
Over $700 million in cryptocurrency has already been restrained as part of these operations. That’s not projected loss. That’s funds traced and acted on.
They’ve also moved to seize domains directly tied to compounds like Tai Chang, effectively cutting off one of the primary ways these operations reach victims.
But what stands out to me is this:
They’re not just treating this as fraud anymore.
They’re treating it as organised, transnational crime with a human trafficking component.
And that changes the level of response.
Why people still believe it’s legitimate
Even with all of this happening behind the scenes, the front end still works — and that’s worth understanding.
These scams are convincing because they combine:
- Professional-looking platforms
- Real cryptocurrency transactions
- Controlled withdrawals early in the process
- Long-term relationship building
From the victim’s perspective, nothing looks obviously wrong.
The platform works.
The account balance grows.
The person guiding them seems knowledgeable.
And crucially, there is just enough “proof” to override doubt.
That’s why these scams don’t rely on quick wins. They rely on time, trust, and controlled validation.
By the time a victim realises something is wrong, the system has already done what it was designed to do.
What this really exposes
What this investigation lays bare is something I’ve been circling around for a long time but never quite had this level of documentation to support.
These scams are not random. They are not decentralised. And they are not small.
They are:
- Structured
- Replicable
- Protected
- Scalable
And most importantly, they are built on a dual layer of harm.
On one side, you have victims losing money — sometimes life-changing amounts.
On the other, you have individuals inside compounds, being forced to generate that money under threat.
That doesn’t dilute responsibility. It doesn’t undo the damage.
But it does expose the system for what it actually is.
Not just fraud.
An organised industry where exploitation is built into the business model — at every level.
Disclaimer: How This Investigation Was Conducted
This investigation relies entirely on OSINT — Open Source Intelligence — meaning every claim made here is based on publicly available records, archived web pages, corporate filings, domain data, social media activity, and open blockchain transactions. No private data, hacking, or unlawful access methods were used. OSINT is a powerful and ethical tool for exposing scams without violating privacy laws or overstepping legal boundaries.
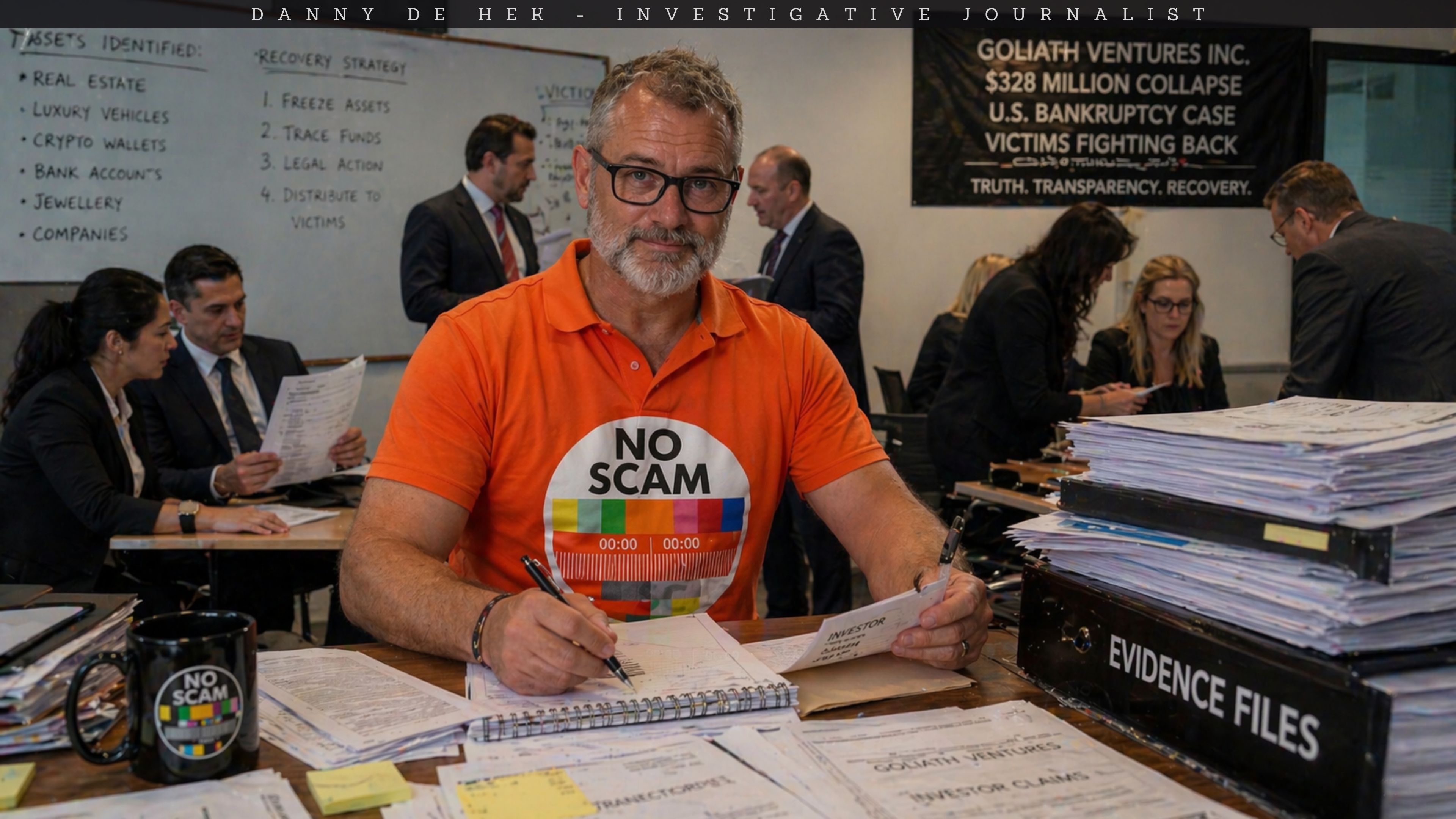
About the Author
I’m DANNY DE HEK, a New Zealand–based YouTuber, investigative journalist, and OSINT researcher. I name and shame individuals promoting or marketing fraudulent schemes through my YOUTUBE CHANNEL. Every video I produce exposes the people behind scams, Ponzi schemes, and MLM frauds — holding them accountable in public.
My PODCAST is an extension of that work. It’s distributed across 18 major platforms — including Apple Podcasts, Spotify, Amazon Music, YouTube, and iHeartRadio — so when scammers try to hide, my content follows them everywhere. If you prefer listening to my investigations instead of watching, you’ll find them on every major podcast service.
You can BOOK ME for private consultations or SPEAKING ENGAGEMENTS, where I share first-hand experience from years of exposing large-scale fraud and helping victims recover.
“Stop losing your future to financial parasites. Subscribe. Expose. Protect.”
My work exposing crypto fraud has been featured in:
- Bloomberg Documentary (2025): A 20-minute exposé on Ponzi schemes and crypto card fraud
- News.com.au (2025): Profiled as one of the leading scam-busters in Australasia
- OpIndia (2025): Cited for uncovering Pakistani software houses linked to drug trafficking, visa scams, and global financial fraud
- The Press / Stuff.co.nz (2023): Successfully defeated $3.85M gag lawsuit; court ruled it was a vexatious attempt to silence whistleblowing
- The Guardian Australia (2023): National warning on crypto MLMs affecting Aussie families
- ABC News Australia (2023): Investigation into Blockchain Global and its collapse
- The New York Times (2022): A full two-page feature on dismantling HyperVerse and its global network
- Radio New Zealand (2022): “The Kiwi YouTuber Taking Down Crypto Scammers From His Christchurch Home”
- Otago Daily Times (2022): A profile on my investigative work and the impact of crypto fraud in New Zealand






Leave A Comment